Permissions
Permissions are used in combination with Roles in Orgvue to control access to resources
This method is often described as Role Based Access Control (RBAC)
Users are allocated to roles which are then used with permissions to determine their access to datasets, properties, packs, views and drafts
Using the RBAC method, the owner or Admin can set the level of other users' access to that resource
Different permission levels are available to use with Datasets, Properties, Packs, Views and Drafts
Note: the role of
adminexceeds any other permissions applied as the logon will be able to view and edit all resources in Workspace as well as manage other user accounts
It is possible to edit the permissions for a single resource (dataset, pack, view or draft) by following the steps outlined in the sections below or edit multiple datasets, views or drafts at the same time by following the steps in Edit Multiple Permissions
To view a video on controlling access rights click the thumbnail to open the video in a new browser tab
Permissions applied to Datasets, Properties, Packs, Views and Drafts are not visible to those roles to whom the permission has been granted
Dataset Permissions
Dataset permissions are entered on the Dataset Metadata screen
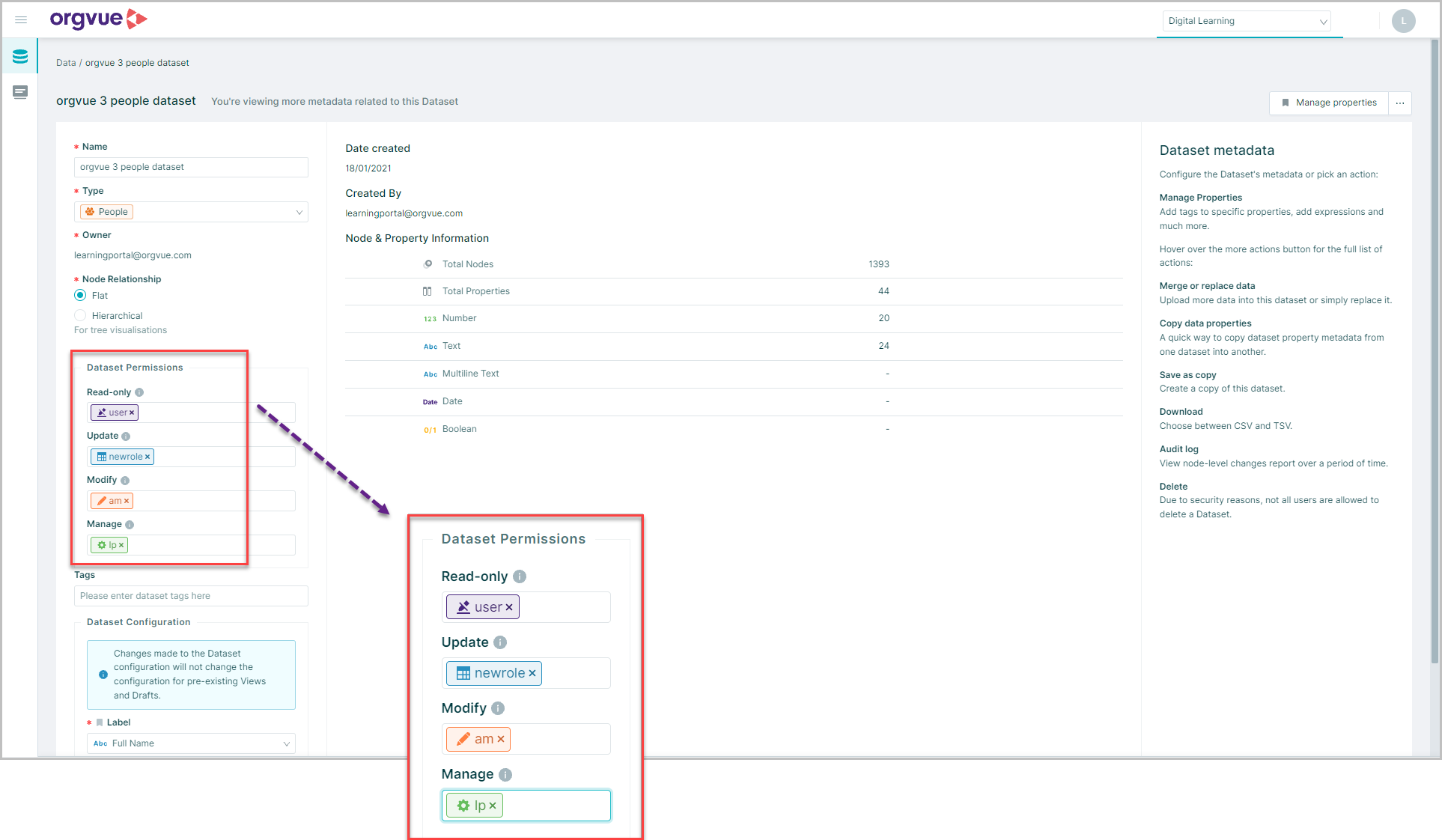
The permission level detailed is applied by adding the role of the user or group affected into the relevant permission field
If the same permission level is to be applied to more than one role these can be entered or selected from the list
Permissions are applied in a hierarchy from most restrictive to least restrictive as defined in the table below
Dataset permissions may be combined with Property permissions to enable further control granularity
| Permission Level | Read Dataset | Update Existing Nodes | Create / Delete Nodes |
Edit Metadata |
Edit Permissions |
Create View |
Create Draft |
|---|---|---|---|---|---|---|---|
| Read only | Yes | No | No | No | No | No | Yes |
| Update | Yes | Yes | Yes | No | No | No | Yes |
| Modify | Yes | Yes | Yes | Yes | Yes | No | Yes |
| Manage | Yes | Yes | Yes | Yes | Yes | Yes | Yes |
- Manage (
manage) is the only operation that lets users create views other than dataset owners
In addition to the permissions listed in the table the permission Update-values may be added as a Tag entered into the Tags box on the Dataset Metadata screen
This is a restricted version of Update which allows the updating of existing nodes only. Nodes may not be added or deleted
Prefiltered Dataset Permissions
Permissions for a Prefiltered Dataset are applied using specific Tags entered into the Tags box on the Dataset Metadata screen
| Tag | Function |
|---|---|
filter-view:{role} |
Added to a dataset to enable Read-Only permission to a Prefiltered version of the dataset |
filter-update:{role} |
Added to a dataset to enable Update permission to a Prefiltered version of the dataset |
filter-edit:{role} |
Added to a dataset to enable Modify permission to a Prefiltered version of the dataset |
However, once entered and saved, these tags will be converted to custom permissions
To view and edit these tags:
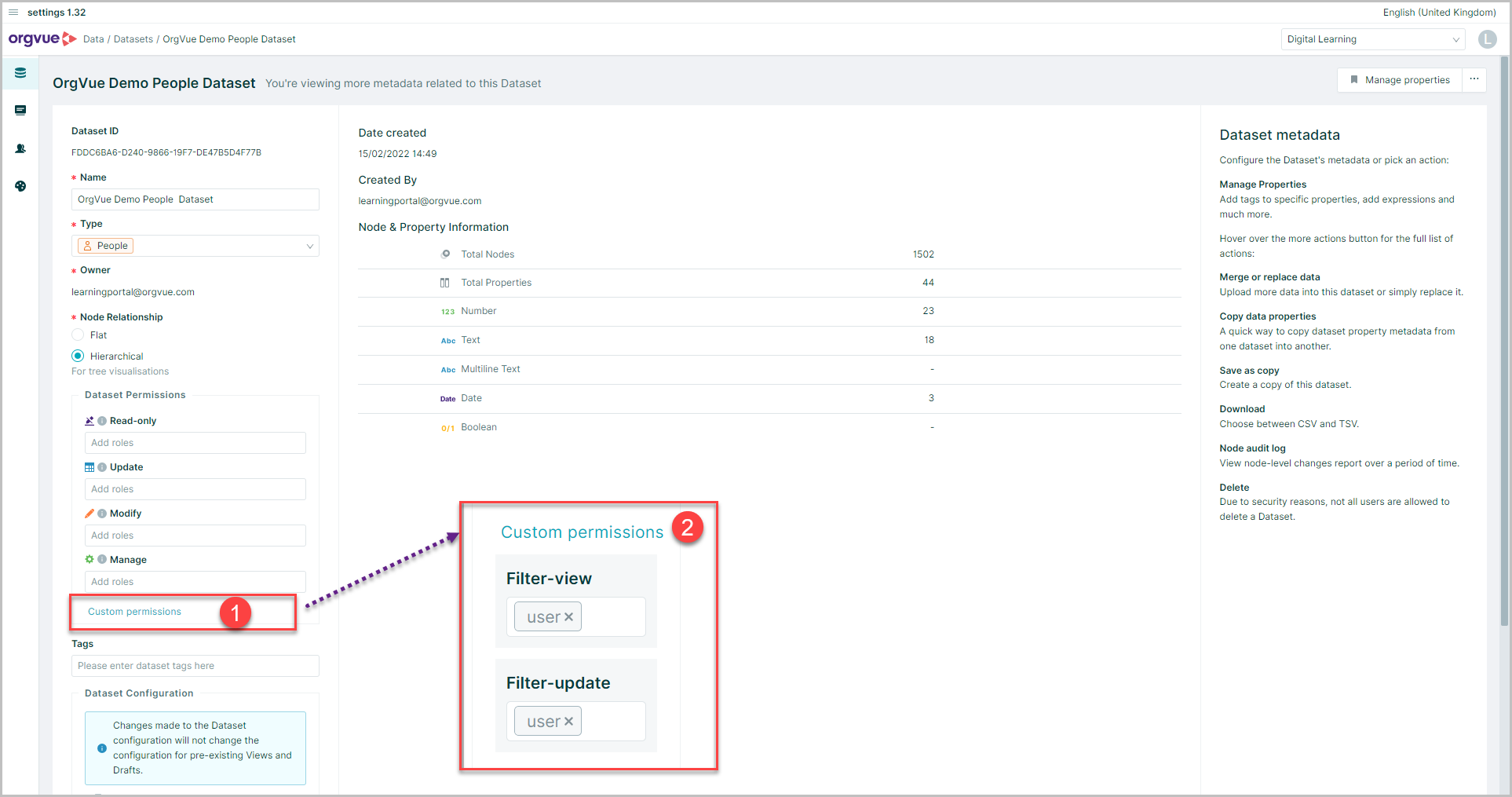
- Select
Custom permissionson the Dataset Metadata screen - The filter permissions will be displayed and maybe deleted or added to
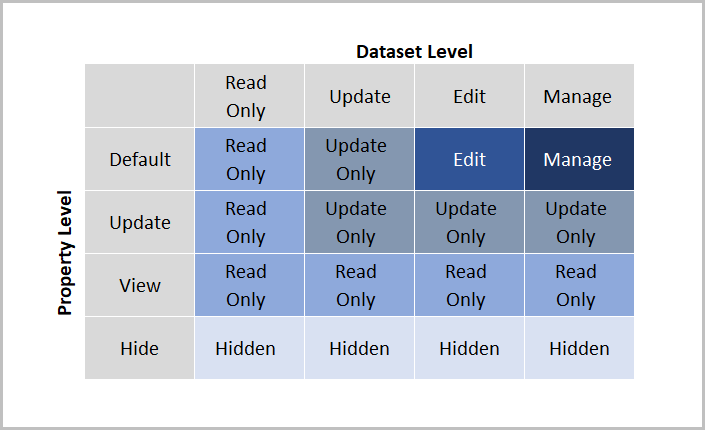
Property Permissions
Permissions may be applied to individual properties within a dataset as well as to the actual dataset
This may be useful to allow all users to see the dataset but hide certain properties from some roles
Property permission are entered on the Edit Property via the permissions tab
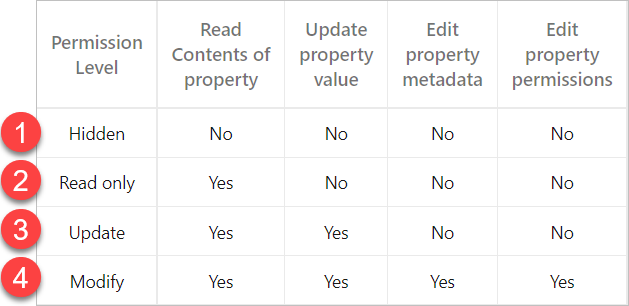
There are 4 levels of permissions that may be applied to properties
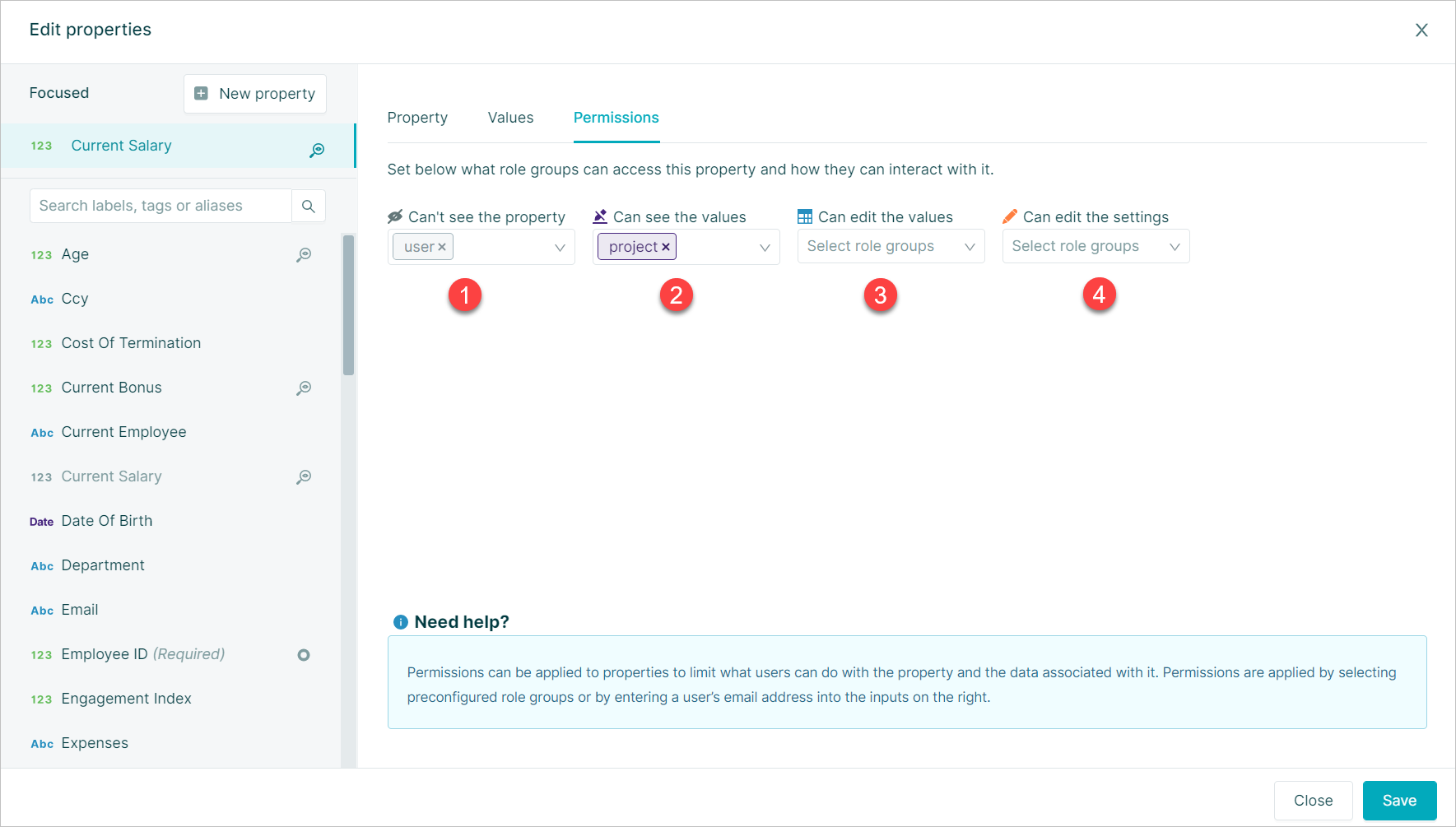
- Hidden: Cant see the property
- Read Only: Can see the values
- Update: Can edit the values
- Modify: Can edit the settings
Permissions are applied by entering a role group into the permission level box
If the same role group is entered into more than one permission level box the least restrictive level will be applied and any role groups in levels below will show faded
Important: When applying property permissions alongside dataset permissions is only possible to further restrict access to properties
E.g. If the dataset has Update permission level set it is possible to apply read only permission to a property
This table shows the relationship between dataset and property permissions
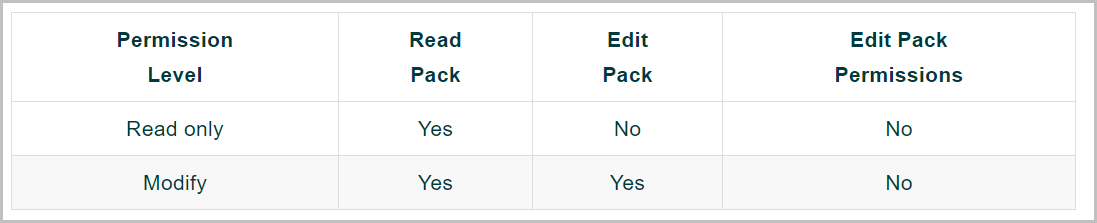
Pack Permissions
Permissions applied to Packs provide access control to the slides and visualizations in the pack along with any pack properties
In addition, a user account will also require the appropriate permission for the dataset the pack is built from to be able to view any data in the pack
Role permissions are entered on the Pack Metadata screen with the required role entered into either:
- A. Read Only
- B. Modify
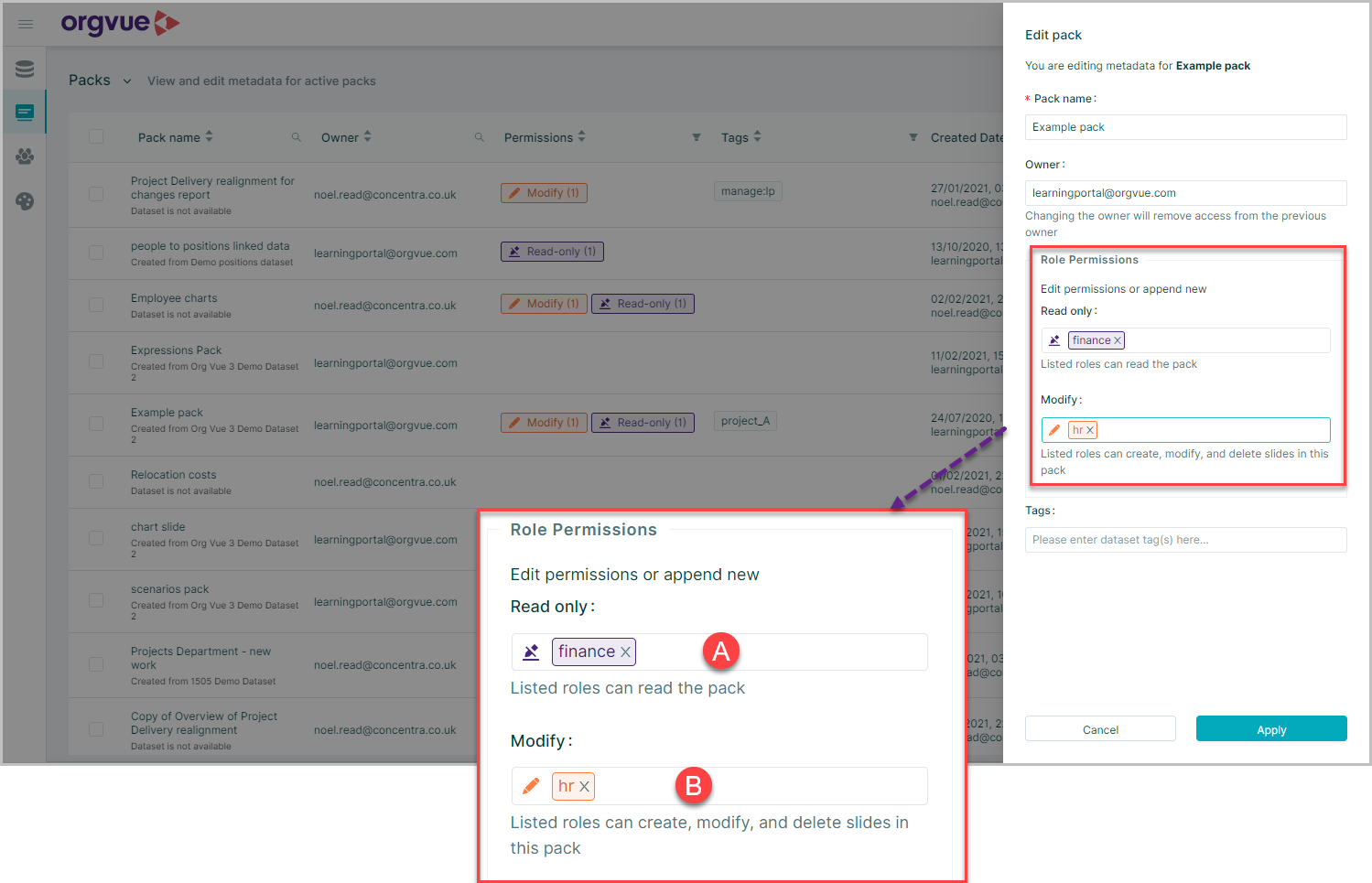
There are only two levels of pack permissions as detailed in table below
View Permissions
In order to create a view a user must be either:
- The dataset owner
- Have the role
admin
Alternatively the dataset the view is being created from, can have a role entered into the Manage field as detailed in Dataset Permissions to enable the specified roles to create a view from the dataset
A View is always Read Only and the Roles or user email addresses of accounts that are permitted to open the view are set during the view creation process on the View Permissions screen
Draft Permissions
Similar to Views, the Roles or email addresses of accounts permitted to view or modify a Draft are set during the draft creation process on the Draft Permissions screen
To import a draft into a dataset requires the importer to either be the dataset owner or have modify permissions for the dataset
NOTE: View and Drafts are the only data items that support user level permissions based on email addresses. Permissions for all other data items (Datasets, Packs, & Properties) are applied using Roles
Edit Multiple Permissions
It is possible to edit the permissions of multiple
- Datasets
- Views
- Drafts
As the same time by:
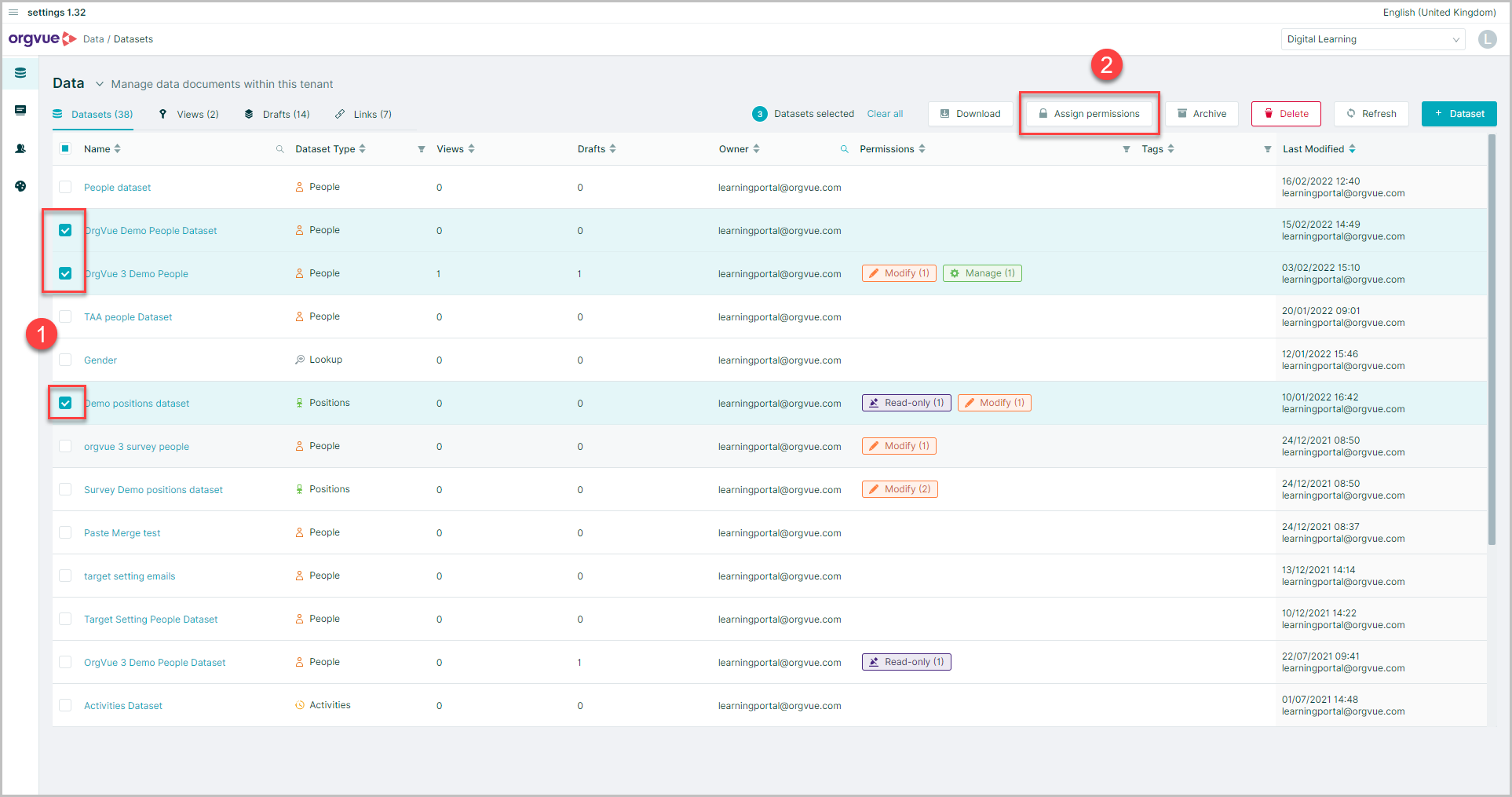
- Select the required datasets
- Select
Assign permissions
This will open the permissions screen for the datasets selected:
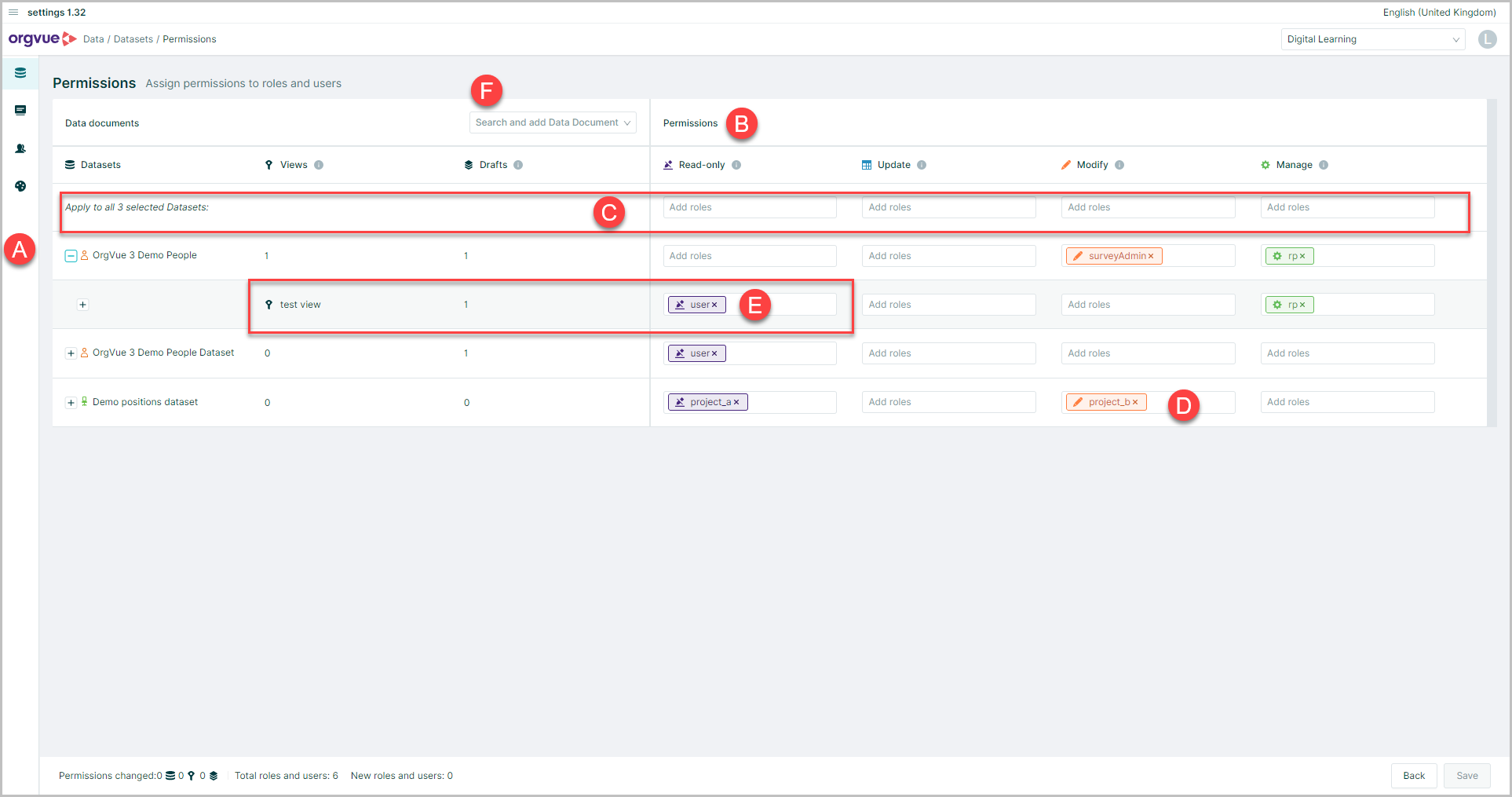
- A. The datasets selected will be displayed
- B. Permission levels are shown
- C. Permissions may be applied to all selected datasets by adding roles into the header row
- D. Roles may be added or removed from permissions of individual datasets
- E. Permissions may be added to views and drafts of a selected data if they exist
- F. Datasets may be added to the selected list
